After a very trying day for many customers around the world that use Microsoft Windows or rely on companies that use Microsoft Windows — like Hotmail/Outlook.com, Office 365, Google Cloud / Compute Engine, Amazon Web Services (AWS), Azure, etc., etc., etc. — we would like to take this opportunity to ensure that our clientele know that we were wholly unaffected by the worldwide chaos.
Is this blog post an opportunistic jab at people who rely on an operating system and company that was late to realise the potential of the Internet? Yes, of course. Why? Well, just look at the trouble that Microsoft gave us last month, and are still giving us today. Microsoft are not our favourite people these days, even though Microsoft themselves weren’t responsible for the Crowdstrike failure.
Hey, we get it, shi … stuff happens. Our status blog currently shows 207 posts in the “incidents” category since 2009. Of course, that’s not 207 failures; at the very most it’s 104 failures if you assume a post announcing an incident and a second announcing it’s over, but in reality some incidents had multiple posts and some posts were only to alert clients to issues with other companies. I’d say that there were far fewer than 100 incidents in fifteen years; feel free to do the maths and check our live uptime monitor for yourself. But one does wonder how an update was pushed out by Crowdstrike without it being tested. That’s just unfathomable. On the other hand, NinerNet doesn’t check every single update we apply to our servers, but we have to rely on our operating system vendors to do that for us. As Crowdstrike customers and their customers found out yesterday, the IT world is very interdependent.
Of course, NinerNet will almost certainly have some major incident in the future, and I know that some will then say that this post will come back to bite us in the ass. Not really. I’m always amused when an incident happens and people say or claim, “We will learn and it will never happen again!” That cracks me up. Incidents — whether they are global IT meltdowns or plane crashes — are almost always human-caused. So yeah, it will happen again, and NinerNet will have some issue at some time in the future and we will learn from it and promise that we will take steps to prevent it from happening again. But we have never and will never claim that it will never happen again.
The other purpose of this post is for marketing. The word “marketing” is a four-letter word to me, simply because about the only skill that marketers have is the ability to lie, with a straight face. I certainly wouldn’t accuse Microsoft or Crowdstrike of any kind of over-marketing or marketing subterfuge but, you know, there’s a part of me that looks askance at claims made by companies that over-promise and under-deliver … and over-promising and under-delivering are pretty much the meat and potatoes of marketers! It is far beyond my remit to determine whether or not either Microsoft or Crowdstrike have ever over-promised or under-delivered, but yesterday under-delivery was rampant.
Update, 2024-07-24: I wasn’t planning to drive home any of my points above, but I was cleaning up some open browser tabs and there were a few Crowdstrike-related tabs still open.
At “Helping our customers through the CrowdStrike outage” Microsoft proudly states, “We currently estimate that CrowdStrike’s update affected 8.5 million Windows devices, or less than one percent of all Windows machines.” Umm, so? Your point is? What they fail to state here is that those 8.5 million Windows devices affected many, many more millions (a billion?) of poor saps who rely on companies that rely on Crowdstrike that relies on Microsoft’s crappy operating system. It reminds me of a saying: “Figures don’t lie, but liars sure as hell can figure!”.
George Kurtz, CEO of Crowdstrike, also stated in a tweet, “Today was not a security or cyber incident. Our customers remain fully protected.” This statement is freaking hilarious! If you can’t turn on your “Windows device”, of course it’s “fully protected”! OMG, this is one for the comedy annals!
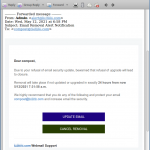
Browsing through Mr. Kurtz’s Twitter feed you see a lot of the aforementioned “marketing”:
* Wow… another great quarter in the books for $CRWD.
* $CRWD delivered a strong 2Q23 with record $218M net new ARR, $2.14B ending ARR, record net new customers & $136M free cash flow.
* $CRWD delivered record Q4 results.
*yawn*